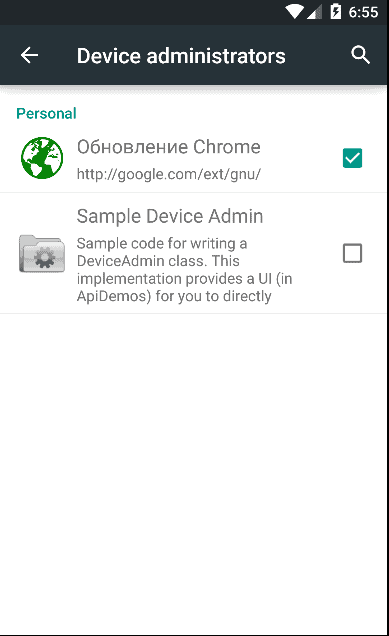
“Our research team has recently seen a large amount of activity in our cloud related to an Android infostealer disguised as a Google Chrome update. This malware is capable of harvesting call logs, SMS data, browser history and banking information and is sending it to a remote command and control (C&C) server. This malware is also capable of checking the installed antivirus applications and terminating them to evade detection.”What makes the malware blend into the android environment is its deceptive name – “Update_chrome.apk”. The troublesome app asks from the administrative access to the system after being downloaded, checks for any antivirus software that might be installed on the device and terminates the security protection, before installing itself without any attention of the user.
 The malware takes cheating to a whole new level by screwing up the Google Play Store payment gateway page to get a hold of your personal credit card information. When the malware is running on the device, the credit card information filled out to purchase an app is instead sent to a Russian phone number, compromising your security completely.According to the researchers at Zscaler, there is no way to remove this latest Android malware without completely wiping clean the device. Since the malware takes over the administrative access of the device, it is virtually impossible to remove it completely without leaving a trace of it behind.Don’t you agree that malware is increasingly becoming synonymous to the Android platform? Is it time for Google to take mobile security up a notch? Let us know your thoughts on the new Android malware below.Source:
The malware takes cheating to a whole new level by screwing up the Google Play Store payment gateway page to get a hold of your personal credit card information. When the malware is running on the device, the credit card information filled out to purchase an app is instead sent to a Russian phone number, compromising your security completely.According to the researchers at Zscaler, there is no way to remove this latest Android malware without completely wiping clean the device. Since the malware takes over the administrative access of the device, it is virtually impossible to remove it completely without leaving a trace of it behind.Don’t you agree that malware is increasingly becoming synonymous to the Android platform? Is it time for Google to take mobile security up a notch? Let us know your thoughts on the new Android malware below.Source:TechNewsToday
Similar / posts
New Android Malware monitors call logs, banking info and more
May 3rd, 2016
Updated on August 16th, 2017
New Android Malware monitors call logs, banking info and more
May 3rd, 2016
Updated on August 16th, 2017
New Android Malware monitors call logs, banking info and more
May 3rd, 2016
Updated on August 16th, 2017